Govern Power Apps in MS Team
Learn how to govern Power Apps in Microsoft Teams including how to prevent Teams Environments from being created.

- Author: Jacqui Peck
- Date: 11 July 2023
Some organisations want to tightly lockdown Power Platform to limit the number of environments created, this includes Dataverse Teams environments. In this blog, I will discuss how to prevent users from creating Teams Environments by governing Power Platform resources within MS Teams.
Users find, add, and pin apps using the "App" icon in MS Teams, from here they are able to share and pin apps to the Teams side-bar or directly into a chat, meeting, or channel. Users can only add and use apps when a Teams admin has allowed the app and it has been made available. Apps that are blocked by Teams Admins appear with a locked symbol in the Teams store but a user can still view and read the "about" info of the app and request for these apps to be approved by admin.

Prevent Creation of Teams Environments:
Dataverse for Teams (and thus Teams Environments) are created when a user creates canvas apps or chatbots within MS Team or when a user provisionsan App Template which are Microsoft out-of-box sample apps such as 'Employee Ideas', 'Milestones', 'How To', etc. Therefore, to prevent Dataverse for Teams environments from being created, admins need to block the provisioning and creation of canvas app and chatbots within MS Teams. To achieve this, MS Teams admins (accounts holding the 'Teams Administrator' role) need to block all the following apps in the MS Teams Admin Centre:
- Power Apps
- Power Virtual Agent
- All App Templates (List of app templates can be found in the Microsoft GitHub repo teams-powerapps-app-templates, note some apps are preview and may not be visible in Teams. These can be identified by viewing the app documentation in GitHub for pre-release)
Individual apps can be blocked at the tenant level using Org-wide app settings or individual app level using App Permission Policies. The following sections explain how to use these settings. Note that org-wide app settings override App Permission Policies. Using a combination of both settings can mean organisation can explicitly allow specific apps or users to use specific apps.
GOVERNING APP IN MS TEAMS:
Three settings are used to govern apps in MS Teams:
- Org-wide App Settings: High-level settings with tenant-wide effect.
- Manage Apps Page: Allow or block individual apps at the org level. The page displays all the available app and their current org-level app status. Here admins can review and accepts permissions individual apps require for all users such as re
- App Permission Policies: App permission policies control what apps you want to make available to Teams users in your organisation. You can use the Global (Org-wide) default policy and customize it, or you can create one or more policies to meet the needs of your organisation.
- App Setup Policies: App setup policies control how apps are made available to a user with the Teams app. Use the Global (Org-wide default) policy and customize it or create custom policies and assign them to a set of users.
- Customised Store: You can customize the Teams app store with your organisation's logo, logomark, and custom background or colour. This will not be covered in this blog, however information can be found in the Microsoft documentation on Customise Teams App Store.
The first two settings (org-wide app settings and manage apps page) allow an app for use in an organisation, the third setting (app permission policies) allow admins to control which users can use a specific app and is controlled on a per-user and per-app basis by creating and applying the policy to specific users.
Organisation-Wide App Settings:
To access org-wide App Settings:
- Go over Microsoft Teams Admin Centre > 2. Under "Teams apps" select "Manage apps" > 3. Select "Org-wide app settings". A side-pane will appear (4.) on the right containing all the available settings. A list of these are in the table below.

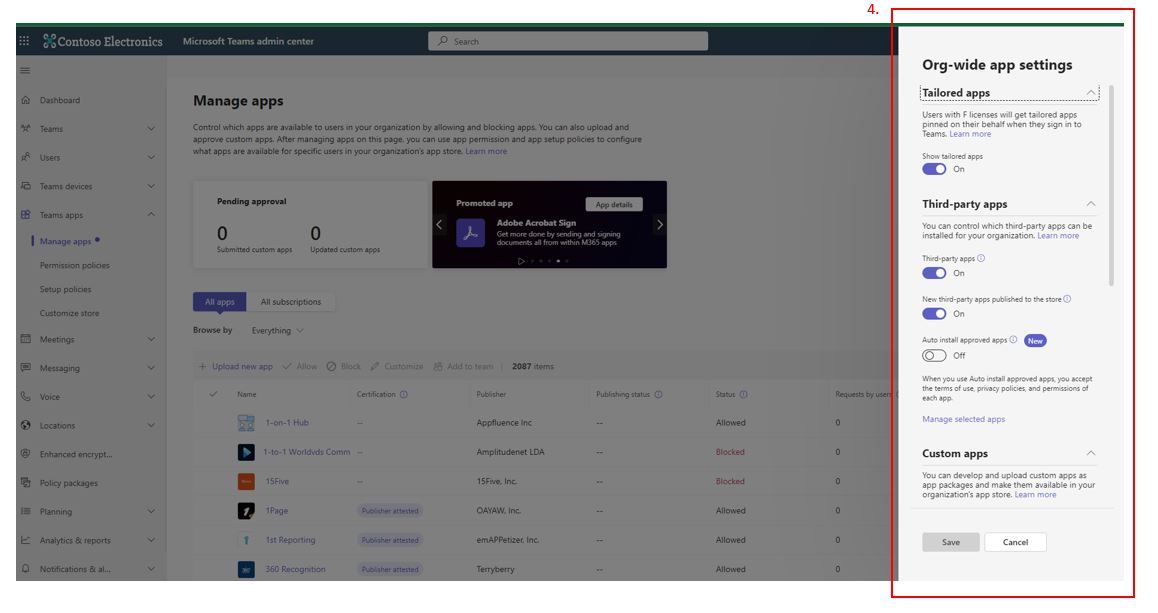
The below table shows the settings available under Ord-wide App Settings (as of 11 July 2023):
| Feature | Setting | Config Option | Default Setting | Description |
|---|---|---|---|---|
| Tailored Apps | Show tailored apps | On or Off | On | Users with F-license will get tailored apps pinned on their behalf when they sign-in to Teams |
| Third-Party Apps | Third-party apps | On or off; turning off will block all users from installing any apps from third-parties | On | Tenant-wdie control if users can install third-party apps. |
| Third-Party Apps | New Third-party apps published to the store | On or Off | On | Will allow new third-party apps published to the Teams store for users, based on Teams apps permissions |
| Third-Party Apps | Auto Install approved apps | On or Off | Off | Selected apps will be automatically installed in Teams for someone when they use Azure AD to sign in on another platform. When you use Auto install approved apps, you accept the terms of use, privacy policies, and permissions of each app. |
| Custom Apps | Interaction with custom apps | On or Off; turn off to block all users ability to use or upload custom apps. | On | You can develop and upload custom apps as app packages and make them available in your organisation's app store |
| External Access | N/A | Link to External access | N/A | Provides info and a link to manage external access in Teams. Users can add apps when they host meetings or chats with external users. The data policies of the hosting user's organisation, as well as the data sharing practices of any third-party apps shared by that user's organisation, are applied. Go to External access to allow or block external domains. |
| User requests Configurations | Customise instructions user will see when they request access to an app | Text field | "this app requires approval from your IT admin to make it availale for you to add" | You can approve user requests for access to blocked apps in the Teams admin centre. |
| User requests Configurations | Redirect request to external URL link | On or Off; when ON a URL field needs to be completed | Off | For organisations that have an established request process, users can redirect to an external URL. |
Manage Apps Page
This is where admins can manage individual apps. To block an individual app in the tenant, from Managed App page (1.), select the target app (2.) and select 'Block' (3.). A warning pop-up appears, select 'Block' again. The app will appear as blocked under status column (4.).
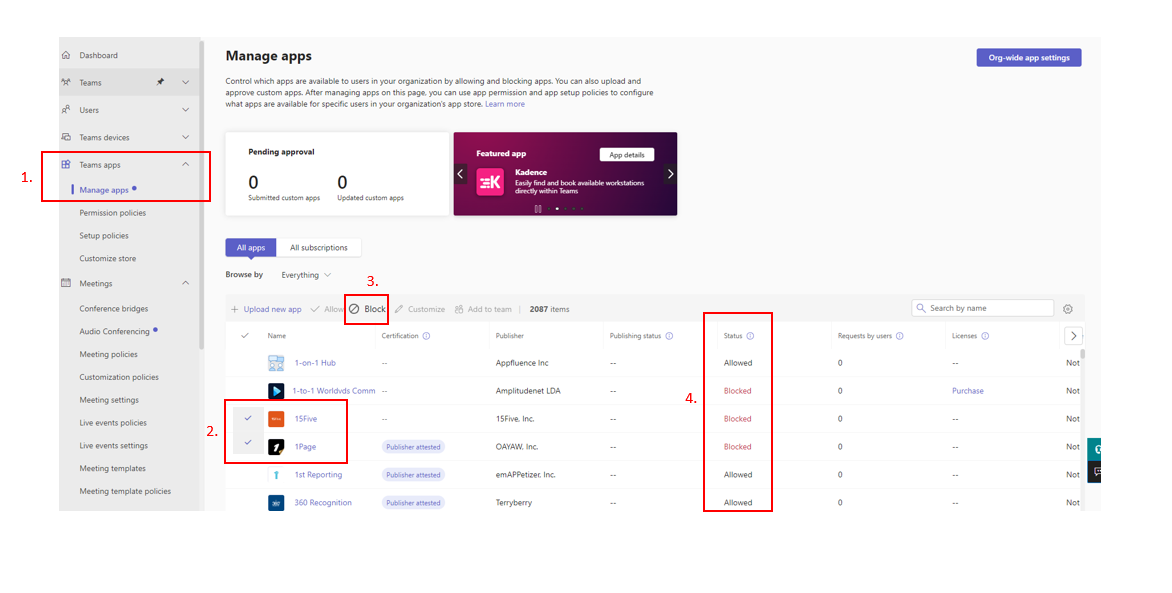
From this page, it is also possible to view and accept app permissions. The process of reviewing app permissions along with any app settings (if available), terms of use, privacy policies, documentation, scope, plans and pricing should be vetted prior to allowing an apps usage within a tenant.
App Permission Policies:
App permission policies control what apps are available to Teams users in the organisation. The Global (Org-wide) default policy is assigned to all users who are not assigned a policy, this default policy can be customised. Alternatively, admins can create one or more policies to meet the specific organisation needs.
Policies can be applied to Microsoft Apps, Third-party Apps, and Custom Apps. The settings (policies) that can be applied include:
- Allow all apps; when selected user can install and use any apps published.
- Allow specific apps and block all others: when selected, admins need to specific explicitly which apps are allowed.
- Block Specific apps and allow all others, when selected admin need to explicitly block specific apps.
- Block all apps, when selected user cannot install apps.
Once a policy has been created, admins can assign the policy to specific users but cannot be assigned to groups.
App Setup Policy
App setup policies control how apps are made available to a user with the MS Teams app. Use the Global (Org-wide default) policy and customize it or create custom policies and assign them to a set of users.
Setting available for App Setup Policy include:
| Feature | Setting | Configurations | Default | Description |
|---|---|---|---|---|
| Custom Apps | Upload custom apps | On or Off | Off | This is also known as side loading. This setting determines if a user can upload a custom app package in the Teams app. Turning it on lets you create or develop a custom app to be used personally or across your organisation without having to submit it to the Teams app store. Uploading a custom app also lets you test an app before you distribute it more widely by only assigning it to a single user or group of users |
| Pinned Apps | User Pinning | On or Off | On | If you turn this on, the user’s existing app pins will be added to the list of pinned apps set in this policy. Users can rearrange, add, and remove pins as they choose. If you turn this off, the user’s existing app pins will be removed and replaced with the apps defined in this policy. |
| Installed Apps | List of apps installed | Can Add or Remove apps | N/A | If you turn this on, the user’s existing app pins will be added to the list of pinned apps set in this policy. Users can rearrange, add, and remove pins as they choose. If you turn this off, the user’s existing app pins will be removed and replaced with the apps defined in this policy. |
| Pinned Apps | List of apps pinned in order | Can Add or Remove apps | N/A | List of apps installed |
Additional Information
Type of apps in MS Teams:
- Core Apps: These are core to MS Teams and come default such as activity feed, chat, calendar, calls, files, etc. Set-up policies can be used to install, pin and control the specific users who can upload custom apps.
- Microsoft Apps: Additional apps created by Microsoft and include some built-in apps such as Lists, Tasks, Praise, Approvals, etc. and often extend MS Teams to other Microsoft products such as Azure DevOps and Viva.
- Third-Party Apps: Apps are built by independent third-party developers and released via Teams store, some of which require subscriptions. All apps released have their security and functionality validated by Microsoft. For information see Microsoft Validation of MS Teams apps and Microsoft Compliance Program which is an optional program for third-parties. Third-party apps in Microsoft Teams aren't controlled or owned by Microsoft and aren't governed by the Microsoft Online Subscription Agreement. Your organisation's use of each third-party app is subject to that app's terms and conditions and privacy statement. Teams admin centre allows you to verify app permissions, privacy statements, and terms of use before you allow its use. As always, you can allow use of an app for a few specific users or all users. For third-party apps, as for custom apps, Teams let admins allow, block, govern, and analyse the use of the apps.
- Custom Apps: Apps created by your organisation are referred to as "custom apps" or "line of business apps" and can include canvas apps and Power Virtual Agents (PVA) chatbots. Apps and PVA resources are created or shared, users can view and install the resource on the Apps page in MS Teams by going to the 'Built with Power Platform' tab under the 'Apps' icon. Users will only see Canvas apps and chatbots if: they created the canvas app or chatbot themselves (or their team owns the chatbot), they have had the canvas app shared with them, or the user recently used the canvas app. Custom apps can be created from App Templates for Teams.
- App Templates for Teams: These are Microsoft created functional and production-ready sample apps that are designed to illustrate a few collaboration use cases in Teams, showcase app development best practices and methods and provide open-source apps that organisation can modify & extended to suit their own business requirements and use within the organisation as custom apps.
- Blocked Apps: Admin can block app in MS Teams, users cannot use these apps but can view the app and its about info. Blocked apps are shown with a locked symbol and cannot be hidden. Users can request to use these apps and require approval by admins, these requests are managed via MS To-Do and the process can be customised to suit business needs. Admins can view aggregate data about number of requests for each requested app therefore helping to make an informed decision about which apps to evaluate for allowing. More info on managing MS Teams app requests. Blocked apps may still have access to data from the teams they're installed in. To turn off app data access, ask your Global Administrator, Application Administrator, or Cloud Application Administrator to turn off user sign-in in the Azure Active Directory admin center.
- M365 Connectors: Connectors in MS Teams are used to deliver content and service updated directly from third-party service into a Teams channel, for example users can receive updates from Trello, GitHub, Azure DevOps etc. MS Teams and M365 Groups use connectors, these are the same for Teams and MS Exchange and are not the same as Power Platform connectors. MS Team connectors allow users to subscribe to receive notifications and messages from web services by an exposed HTTPS endpoint to the service to post messages in the form of cards. As long as a team member has add/remove permissions can modify connectors setup. If the user who added a connector leaves the team, the connector will continue to work. There are a list of connectors that cannot be configured. M365 Connectors and Webhooks are similar in that they use HTTPS endpoint, read about MS Teams Webhooks and Connectors.
Ways to manage apps in MS Teams:
| Function | Location | Permissions | Comments |
|---|---|---|---|
| Admin App (canvas app) | download from MS Teams App Store | Global Admin, Teams Administrator, User Administrator, and Billing Administrator | Designed for small businesses as a centralised hub for managing M365 within MS Teams. Provides simplified view of common used & request admin tasks such as users, subscripion, grand access to services in M365, and change setting sin MS Teams meetsing, messages, files, and webinars etc. |
| Manage App | MS Teams Admin Centre | Global Admin or Teams Admin | A sub-feature in Teams Admin portal specifically used for managing apps within MS Teams. |
Manage Custom Apps in MS Teams:
Admins control the rollout of and access to custom apps using app policies and admin centre settings. To block custom apps: ensure the setting 'Interaction with custom apps' is disabled (off).
Disabling M365 Connectors in MS Teams:
Admins can use Exchange Online PowerShell to disable connectors for an entire tenant or specific group mailbox, but not for specific users. If a connector is disabled, it affects all users in that tenant or mailbox. Tenant settings override group settings. Exchange Online PowerShell v2 module uses modern authentication and works with MFA to connect all Exchange related PowerShell Environments in M365. See Microsoft documentation on how to enable/disable connectors in Teams using PowerShell to configure the SetOrganizationConfig setting.
To disable M365 connector for tenant:
- Set-OrganizationConfig -ConnectorsEnabled:$false.
To disable actionable message for the tenant:
- Set-OrganizationConfig -ConnectorsActionableMessagesEnabled:$false.
To enable connectors for Teams, execute the following commands:
- Set-OrganizationConfig -ConnectorsEnabled:$true
- Set-OrganizationConfig -ConnectorsEnabledForTeams:$true
- Set-OrganizationConfig -ConnectorsActionableMessagesEnabled:$true